In this Episode
- [02:24]Tom discusses what he believes we regular people need to do to protect ourselves from a privacy and security standpoint. In his answer, he points out that the world is changing around us, so we need to change with it.
- [04:17]Security is more and more a part of the public psyche, Tom explains. He then talks about ransomware, which generally happens to people through phishing.
- [08:46]Stephan recaps what Tom has been saying to make it clear for listeners. Tom then expands on what Stephan has said.
- [10:01]Is there insurance to cover losses through phishing and similar scams?
- [10:35]Stephan gives an example of a very clever phishing technique that may have caught people off-guard. Tom then gives another example.
- [12:51]Stephan’s aunt was scammed not too long ago, he reveals.
- [14:20]We hear about another example that Stephan has seen in a Black Mirror episode, which Tom reveals is taken from real life. Stephan and Tom then talk about putting bandaids or tape over computer cameras.
- [16:35]Tom shares some ways you can better protect yourself. The first of these is to stop giving things away and make conscious trades about privacy invasion, which he discusses in great detail.
- [19:42]You can sometimes change permissions, Stephan explains. Tom then points out how hard these settings often are to find.
- [22:46]Another step in protecting yourself is by making it harder for the bad guys. People are generally using better, more complex passwords now — but the problem is that they are now using that one complex password everywhere.
- [26:06]Tom advises lying in one particular instance: the security questions for forgotten passwords.
- [27:22]There is one foolproof way not to click on dangerous links in phishing emails, Tom explains: don’t click on any links. If you get an email from your bank, for example, close that email, open a new web browser session, and go to your bank’s website directly.
- [29:00]What does Tom think about password managers to keep track of your various complex passwords or passphrases?
- [30:36]Tom offers another piece of advice, which is to turn off your computer and leave your phone outside the room if you’re going to have a sensitive business conversation. Computers can easily be turned into bugging devices.
- [32:13]How does this work in terms of devices such as, for example, Amazon Echo? Should listeners get rid of these devices?
- [34:20]Tom shares another easy, free step to be more secure: turn off automatic images in your email.
- [35:27]Tom differentiates between malware and adware. Stephan then talks about an example of nasty adware.
- [37:25]Does Tom have tips or tools for how to remove adware or malware?
- [39:24]We learn more about two-factor authentication and biometrics. What’s coming into play in the future, though, is behavioral biometrics, which Tom explains in some depth.
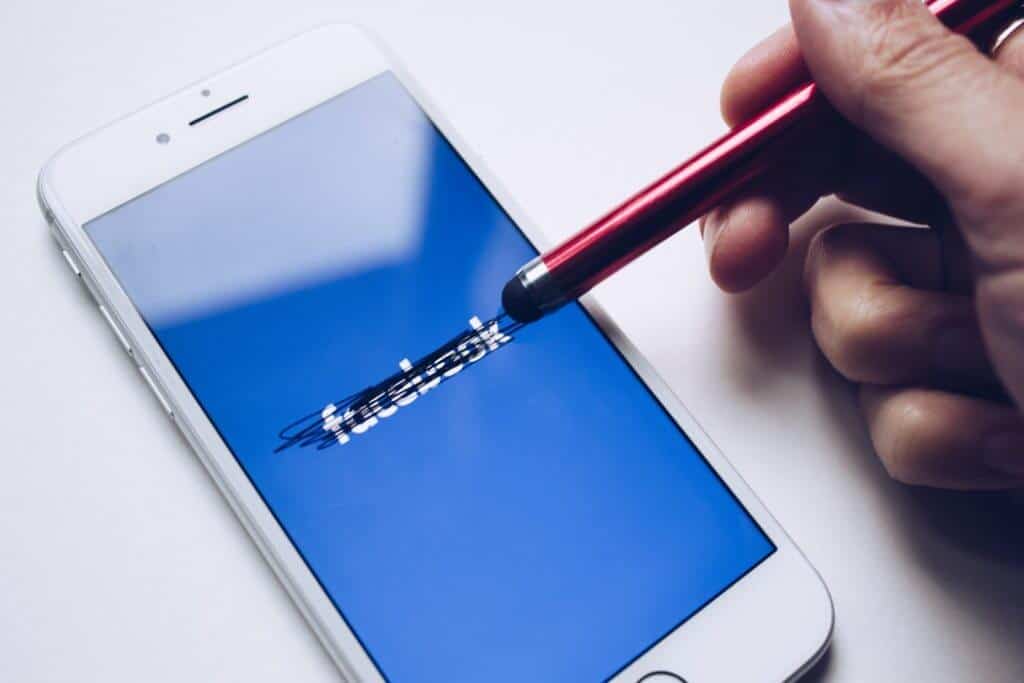
- [43:01]Stephan points out why two-factor authentication is particularly important for Google and Facebook.
- [44:33]What is the Dark Web, and why should we care about it?
- [46:59]There are a dozen or so anonymous currencies used on the dark web, of which Bitcoin is the most popular.
- [48:00]Tom talks more about Bitcoin
- [49:43]We learn more about finding things on the dark web, which often requires you to build up a dark web reputation first.
- [51:08]What tips would Tom like to recommend in terms of protecting yourself from identity theft?
- [53:40]Tom talks about his high-level security clearance, touching on how people can get cleared and what the downside is. He also shares the advice that he gives to teenagers.
Tom, it’s great to have you on the show.
Hey, I’m really happy to be here.
It’s a real honor because you are a super ninja guy. You advise governments and the administrations, and so forth, on how to be secure and how to infiltrate different nefarious cells and things like that. I really appreciate you taking the time to chat with us on this podcast. I’d love to hear what you think the future holds in terms of just us regular people, what do we need to do to protect ourselves from a security standpoint, from a privacy standpoint? It’s a really scary world out there and it’s getting scarier each day with the technology that’s advancing and the capabilities that bad actors have in going after us and accessing all of our stuff. Let’s start there.
It’s a great place to start. My role is Chief Trust Officer at Unisys. I spend the entire focus of my waking hours helping anyone from a government to what I would call critical infrastructure company down to key individuals better protect themselves in this new digital world we live in. The first thing I like to stress is if you’re not doing everything right today, that doesn’t mean you’re at fault or you’ve made mistakes. It means that the world is changing around you and all we’re asking you to do is change with it. The whole concept of what you do digitally has changed so dramatically from just a few years ago that you have to change the way you look at security and privacy with as much change as you do with the way you operate. You’re doing banking online, doing your taxes online. It’s just scratching the surface. Now, your cars are driving you home, your houses are waking up when you walk in, everything is being monitored with your Fitbits. Your whole digital footprint has changed dramatically so what we’re asking people to do is rethink how they look at security, what their role is. This is not something where either a big brother or a big company is there to protect you. It’s really up to the individual to take steps. The good news is there are plenty of things that individuals can do better to make themselves much, much safer and much more in control of their privacy.

What would those things be? Actually, before we dive into those things, let’s talk about some of these risks because folks may not be familiar with some of the recent tactics for phishing and social engineering and so forth. They may not even know what those words mean so let’s start there and then we’ll talk about the remedies and protections.
It’s seeping into popular culture where security used to be sort of the geeks on the side. We talk in whisper under the rose. Now, it’s on primetime television, it’s on the front pages of your newspapers, and then it’s the lead stories on your network news so I think it’s becoming more and more in the public psyche but you’re right, they may not know exactly what that means. One of the biggest threats today in 2017 that didn’t really exist in the prior lifetime is what’s called ransomware. This is where all of your digital stuff, whether it’s on your laptop or your phone or in the cloud, all of that, someone comes in and encrypts it so you can’t get to it but they can and then they offer to sell you the decryption key for all your stuff for $500. They pick $500 because they figured it would cost you more to hire some professional to grab it back for you or do anything else. $500 is just about the right number that they’ve optimized. People will pay for it. If you didn’t make a backup in advance and you didn’t take basic precautions like patching your systems, you’re going to be susceptible to ransomware. It is very, very widespread. It started out as something that was done to a select few and now, the tool kits to do it are available free on the internet. That means anybody with an internet connection and a borrowed computer can launch a ransomware attack against you. You need to be aware of that. That ransomware is certainly one thing that’s growing and unfortunately, it’s growing not only for individuals, but it started to move last year and now it’s in full force in being addressed to two new groups.
One is companies, like an entire hospital, had all their stuff encrypted and they had to pay a bigger payment than that in order to get it back and even more worry some in some power companies, energy companies, their industrial control systems, the machines that actually move the electricity around the grid and open and close the gas pipelines. Those machines were being encrypted and held for ransom with the same kind of ransomware technology. Ransomware is certainly something that’s touching everybody. It really needs to be accounted for as you go around and defend yourself. The way you get it, sort of the old model of calling everything a virus which we evolved beyond but the way you catch this particular ransomware malware is generally through what’s called phishing. Phishing is just an email. Most of your listeners are familiar with spam emails but many of them equate them to really poorly written, they fall into a couple of things, my Nigerian Prince just left me a billion dollars and I’ll split it with you kind of emails that are so obviously laughable. But most of your listeners know not to click on those.
What they may not know is today’s phishing, even more to a point of what’s called spear phishing where they pick out a message just for you, crafted just for you, with indicators that talk about your family members, or your job name, or places you’ve just been recently that you shared on social media but phishing and spear-phishing has gotten so good that you can no longer just look at the email and say, “This one’s legit and this one’s not.” The phishing that’s coming now is trying to do anything it can to get you to click on a link and it will say things like, “Hey, this is your bank. We’re with the Bank of Pacific of California,” which is one I just made up, “and we saw that there’s been suspicious activity in your account. Click here to reset your passwords.” If you happen to have a bank account at that bank, you’ll think, “Hey, that’s good of them to tell me there’s suspicious activity. I’ve heard that there’s a lot of malware going around. I’ll clink on that link and reset my password.” In fact, what you’re doing is giving the bad guys your ID and password once you click on that link. Phishing attack has gotten very sophisticated and there are some specific things that everybody should be doing to combat that kind of attack. Ransomware and phishing attacks certainly are two of the big ones in 2017 for consumers.
Ransomware and phishing attacks certainly are two of the big ones in 2017 for consumers.
Basically, what would happen is that you get this email, it looks legit, and if they’ve taken the extra effort to identify some personal attributes about you or family members, they can spear phish you and make it seem like it really is legit. It doesn’t have typos or anything or weird grammar mistakes and you think it’s real and then you click to login and you’re not logging into the bank’s websites. It’s the evil bad actor’s website.
It will look just like the bank’s website with all the right logos, and everything, the right place and they’ll say, “Please type in your old ID and password first, and then we’ll help you reset it.” As soon as you type it in, within seconds, there are people on the other side of the world reading that as soon as you type it in, and within a minute, all of your money has been cleared out of that account.
You can’t get it back, right? It’s gone forever.
It is difficult. It changes by what country and what laws protect you and what kind of account you have. In some cases, the banks will give it back to you but in many cases, people just lose it. That’s the problem.
Horrible. Is there insurance to cover this sort of loss?
There really isn’t. There’s a new category of insurance called Cyber Insurance but it is not all the way thought through yet. It’s really not proven yet to be terribly effective for people.
Wow. It’s so scary. There’s really not a lot you can do if you got scammed.
Let’s go back to the original. There’s not a lot to do after you’ve been scammed. There is a lot to do to stop from being scammed. That’s one of the things I really hope we can cover later.
For sure. Before we dive into those protections that we can institute in our daily lives, things like two-factor authentication and so forth, let’s give an example of a very clever phishing technique that might’ve caught people off guard and they weren’t expecting it. I just recently read about this, it’s targeting Gmail users. It looks like a legitimate email and then there’s what looks like an attachment. You know how Gmail formats their attachments. There’s a particular look to it at the bottom of the email message. They add what looks like an attachment but it’s an image and then you click on that and it takes you to a page that looks like a Google page but now you’re being asked to login again. That’s not a Google page and when you log in then they have access to your Google account. With that, they can lock you out and they can access all sorts of other services that you’ve used. I’ve lost my password too, please send me a new password and they have your Gmail account so they can make all those requests and reset all those passwords and again, empty your bank account and whatever else unless you got two-factor authentication. Is that a good recap of an example?
It is. It’s becoming almost standard. They get even more sophisticated than that. A very common one now that we’ll see is they’ll say, “I was talking to your uncle Joe this morning. He showed me this file and thought you’d like to see it.” He found out you had an uncle Joe because you posted it on Twitter, or Facebook, or Instagram, or something. They’re really doing everything they can or, “Hey, I see you work at XYZ Corp. This is something that a bunch of your XYZ Corp. colleagues are doing. Click here.” Those kinds of things tend to make it more personal. People have already seen this in online advertising. They go through whatever your social media choice is through the ads say, “Your friend Suzie likes this. Don’t you want to see this ad too?” You start to say, “Oh, Suzie likes it, it must be good enough for me.” The bad guys are doing the same thing with phishing. It’s really up to everybody to take better precautions so they don’t fall victim to this.
You’d be surprised how many people fall victim to this stuff. My aunt was scammed not too long ago by an email where a friend of hers supposedly was in London on a trip and she had her passport stolen and all her money. She didn’t have a way to get her money and she thought, “I should contact Stephan’s aunt.” She didn’t think to check out the story. Is my friend actually in London? No. She never was in London. It was the scammers who sent this email. So she went to Western Union and wired some money to the scammers.
Making people aware generally of those kinds of tricks is a public service.
That’s a trick that’s been going around for over five years and yet people still fall for it. Making people aware generally of those kinds of tricks is really a public service that you’re doing here because if you’ve seen it before, you know to be suspicious. It’s almost always a relative, they’re stuck, they’re in a foreign country, and they just need a few thousand dollars. If 1 million people delete it and say, “That’s stupid. I know that’s a fake.” They’re fine with that because the 1,000,001st person out there says, “I better run and wire them some money.” That’s all they need. It costs them nothing to send it out to a million people. They just wait for someone to fall for it. The more we can make people aware of these kinds of scams, the better it is for everyone.
Another example that seems kind of similar to ransomware that I think is going to rise popularity with the bad actors, I don’t what the name for it would be, maybe extortion ware but I saw a Black Mirror episode. It was about extortion ware essentially where this kid was being filmed after getting malware. He was doing something that was very embarrassing and so the bad actors made him do stuff to not release that video out on the internet and they ended up doing it anyways even after he did all these bad things that they taught him to do. Did you ever see that episode?
Yeah, I did. The Black Mirror, I think they’re great, sort of futuristic. Not too distant futuristic. Look at the future we might all enter into soon. But that particular episode was actually taken from real life. That actually does happen on a fairly regular basis. The thing to do there is if you get one of those emails is to call the FBI. They do know what they’re doing in this case. They can immediately pounce on it. Just as any episode, it’s likely to be released anyway so giving them more and more is the wrong thing to do. FBI takes cyber crimes very, very seriously. In this case, they’ve got a whole cyber division that knows exactly what to do when you get cyber extortion like this and will be very, very helpful in protecting your privacy as well as catching the bad guy.
Simple, really simple protections like putting tape over your camera on your laptop will help protect your privacy.
I have band-aids over the cameras on all of my devices, all my family’s devices. Band-aid works well. It’s got that soft cushion so it doesn’t get sticky stuff on your camera when you peel it off and it costs $.10 so easy enough to open and close and control who can see through your camera.
Even Mark Zuckerberg has tape over his camera. I saw an article with a picture of his laptop and zooming in, you could see there was tape on his camera. It makes a lot of sense. Let’s talk about some of these protections now.
Sure. There are a lot of things that don’t cost anything and they’re easy to do. It just takes a little bit of a change. I have them in a few categories. The first one is stop giving your stuff away. Way too often when someone says or you’re looking around and you there’s this new app for your phone or for your computer. Up comes the screen after you choose it and before you install. The screen says, “Do you agree to these permissions?” It’s a long, long list of fine print. You just keep hitting approve, approve, approve as many times as it asks until the app loads, right? That’s how you do it. That’s how everybody does it. What I ask you to do is look at those things because in 99 out of 100 cases, those companies are over asking. They may need access to your calendar in order to post things if it’s a calendar app but they shouldn’t need it if it’s just a game. What’s happening is nothing is free in this world. You’ve all heard the adage, if you’re asking how they make it for free, that means you’re the product. Someone’s getting your information and selling it.
If you’re asking how they make it for free, that means you’re the product. Someone’s getting your information and selling it.
So these free apps, whether they’re games, or little social media helpers, or all sorts of apps, there are I have to say, millions of apps available, most of them, they’re harvesting the information that you freely trade away in exchange for that app. In many cases, people are making a really, really bad trade. They are giving away access to turn on your camera at anytime so they don’t have to hack in, you’ve given it away. They’re given away access to listen through the microphone at anytime. They’re given access to take copies of everything in your database of contacts and share that with anybody they want at any time. These are things that are so overreaching, that if you read it, you probably would not make that trade. Since there are millions of apps, there are probably other versions from other groups that will give you the same functionality without over asking, without overreaching.
I ask people, just look through. Some of these are going to make the trade anyway. If you want the popular social media app, you’re going to agree but understand what you’re agreeing to. Your amount of data that these social media companies capture on you goes well beyond what you click like on. It’s amazing how much data you give up through things like your GPS chip, the accelerometer in your phone. You’re giving away access to all that and companies are making a fortune taking that information about you and reselling it. First and foremost, just look at the trade. When you download something, make your own conscious decision, “Am I going to trade this much privacy invasion for this app?” If so, say yes. In which you will, in many cases. But in a few cases, maybe you’ll start to say, “Hey, it’s just not worth it to me. That’s way too much stuff I’m giving away to a group I don’t know anything about for this app that I could probably live without.” I’m asking people to think through that trade and make sure it’s something that they’re really comfortable with in terms of giving up their privacy.
That makes a lot of sense. A lot of times, you can change the permissions too. When a tool asks for access to your Facebook, or Twitter, or Google, then you get this next screen which is from Twitter saying, “Do you want to give access? These are the permissions.” You can oftentimes go in and change the permissions and only give permission for example, “Can this app post to your Twitter on your behalf?” You could say yes but only to yourself instead of your friends or to the public.
But they make these choices deliberately difficult to get to, cumbersome to get to, because they want people to give away as much data as possible because that’s how these companies make money. They’re pretty straight forward. They’re business model. There’s a reason these social media companies are worth billions and they’re called unicorns. Because they don’t charge you anything, they figure out a way to harvest so much data from you and monetize that/ not just these apps. I have a Vizio TV in my den. One night, at [3:00]AM, that popped a little box that says, “Press okay to approve the new privacy settings.” There wasn’t an option for not pressing okay or to review the privacy options. The only option was to press okay on your remote. I didn’t. The next day, I hacked my way through and looked through and found what they were asking for. It turns out they have already been and were asking to continue to read what was on my screen at every given time, mapped that back to what shows I was watching, and then sell that information to anybody that they could make money with. You got to think about what trade you’re making when you do that and then go through the hassle of figuring out how to be specific about what privacy you’re willing to give up. In that case, I finally was able to tell it that I was not willing to have them share that information so they stopped but they’ve been doing it for years. They just got caught. They’re not alone. All sorts of product vendors are capturing as much data as they can get away with. In every case, figure out what you’re asked to give up and then go through the process of thinking it through, and if you’re willing to do it in exchange for free apps, and free games, and more real-time television, then that’s great. I just want people to make a conscious decision.
For sure. I remember reading about that Vizio scandal essentially because they weren’t telling people that they were doing this and then they got caught.
Even when it became public, the remedy was, “Click okay to approve.” Not, “Read this. Here’s what we’re doing. If you like it, click yes. If you don’t like it, click no.” I wish more companies that deal in this space would be more upfront but until they are, it’s really up to the consumer to understand that trade and to make their own decisions.
That’s the first step. Don’t give away your permissions and access to all your data without at least thinking it through. What’s the next step?
Make it harder for the bad guys.
The second is just make it harder for the bad guys. Most people by now have a really good password. Most people that I know, the friends of mine no longer use password as their password or 123456 as their password. That’s now down to less than 15% of the passwords are 123456 or password. They used to be over 50% worldwide.
Wow.
They’re getting better at having a great password. What we’re not getting better at is making the mistake that people use that single great password everywhere because it’s so great. The problem with that is because they use it in many cases because your work access requires now a complex password or one of your systems requires a complex password. You can say, “Well, I’m not going to remember something crazy like that. I’m going to remember one and I’m going to use it everywhere.” The problem is that a lot of these other places you use it are also getting hacked themselves. What happened recently was LinkedIn, which most professional people have a LinkedIn account. It’s got their ID and their password. If it’s that same good password, the moment it was hacked from LinkedIn, the hackers don’t go in and try and change your update status. They couldn’t care less. They go to every bank site in the world and try that ID and password combination, in every job site in the world and try that ID and password combination, in every other thing that can monetize quickly with your ID and password. If you reuse that really good password in multiple places, you’re just asking for trouble because not everybody takes perfect care of your sensitive information like passwords and it is getting out. It’s gotten out from many social media sites already and it will continue to get out so all I ask is that people don’t use the same great password in every different place because that will make it a lot harder for the bad guys to steal your stuff.
This happens because a lot of the sites have bad security and instead of storing a hash of the password that you supplied, they will just store the password in clear text.
I don’t want to say bad because it’s where companies have to evolve quickly as well. Many of these companies are encrypted, they’re just not encrypted with the most modern stuff. Not everybody keeps up with that. They just implore people to take matters into their own hands. Someone hacks my LinkedIn account, they’re only going to get my LinkedIn account. They’re not going to get access to my bank account or my job. Just keep a different one. I recommend moving beyond the content of a password and start thinking about a passphrase. It’s really not that much more difficult. I do a person, place, and thing. Think of a person in a particular place involved with a particular thing. Anybody can do this then it becomes something that’s very memorable. Say a person, place, and thing for LinkedIn and then you got it. That’s your unique thing. And then you pick a different person, place, and thing for someone else in some other site. It’s not much harder to think of it as a passphrase instead of a password. In the end, these are the things that don’t cost anything.
Another way to do is to lie. I’m a good boy and I was raised right but there’s one instance where I ask our listeners to lie. That is these backup questions for if you forgot your password. Companies today still ask name questions like what is your mother’s maiden name, what is your hometown. If you answer those honestly, you’re just asking to have your password stolen because that information is readily available either through a Google search or a dark web search. It can be found in a matter of seconds so anyone could call up and say, “Hey, I’m Steve. I forgot my password. Can you reset it?” They’ll say, “Okay, what’s your mother’s maiden name?” “Oh, it’s Smith.” Boom! They’re in and they’ve got your new account information. I ask in this case for people to lie. When you’re asked a name question like mother’s maiden name as password backup, they deserve to be lied to because they shouldn’t be asking you questions like that that are Google-able.
In this case, just pick something else. If they ask my mother’s maiden name, I’d come up with my favorite car or if they ask what high school did I go to, I come up with my favorite vacation town. Just pick something different that you can remember and you’ll be much safer for it. The third and final one is those emails, those pesky phishing and spear-phishing emails that everybody’s getting now, there is one foolproof way not to click on the bad links and that is simply not to click on any links. If you get an email from your bank and it looks terribly legit, and it says, “Look, this is really important. This is not phishing. This is really important. We need you to log on and reset your password because someone is about to steal all your money.” You’re pretty sure it’s real so the thing to do is to close that email, delete that email and open up a separate web browser session and go to your bank and login directly. If they really have something urgent to tell you, it’ll show up when you log on to their site. Most of the time, it still is a fake and it’s just the world we live in. I’m in the habit now where I don’t click on anything. My friends know not to send me Christmas cards with links in them because I just won’t click on them. I’d much rather have a little text message that said, “Hey Tom, think you can be over the holidays?” That is much more meaningful than, “Hey Tom, click here which may or may not be malware that cleans out all your banks.”
Yeah.
Lie about your backup questions and don’t click on anything in an email ever, ever.
Those three make it harder. Have that great password but switch it to a passphrase and make it different for each place. Lie about your backup questions and don’t click on anything in an email ever, ever.
That’s great advice. What do you think about passwords managers as a way to keep track of all these different unique passwords or passphrases that you’re creating for all the different sites that you have access to?
I know a lot of people use them. I personally worry about any aggregation site where I’m going to put all my sensitive information in regardless if they are government-grade or military-grade or whatever these companies say. I don’t like the idea of putting it all together into one place. I have actually found that using the passphrase concept and making little notes on LinkedIn, let’s say I used a person, place, and thing of Fred that I went to Tunisia with and bought malachite. So fredtonishamalachite would be my password. All I have to do in my Outlook is say, “LinkedInPWDequalstunis.” That’ll remind me, oh that was the one about Tunisia. You can have little reminders that mean something to you for this passphrase as long as you get comfortable with what the three pieces of your passwords are. I found that to be very workable and so I’ve stayed away from any password managers and just have a fear of going to an aggregations point.
Got it. I’m using one password and I really like it.
It’s working and it works for a lot of people. It’s just that for me, if it gets more complex than it is today, I’ll go that way but honestly, the industry is moving to quickly get rid of IDs and passwords and favor what’s called behavioral biometrics. So in another couple of years, you won’t have passwords to worry about anymore. I’m betting on technology to get us out of this space.
Wow. Behavioral biometrics, we’ll have to talk about that in a minute but what else should we do? What are the other steps in this process?
If you’re going to talk about something that’s actually business important or highly sensitive, I encourage you to close the laptop clamshell and power off the computer. It is pretty easy now to turn those into bugging devices. We just had an incident where 70 companies were targeted or just the C level executives were targeted. They turned on the microphones in their laptops and just recorded 7 by 24 and then built in an artificial intelligence program to call through all those files, looking for sensitive stuff that they could make money off of. That’s not hard to do. The tool kit’s free and plenty of people have access to it now. It’s fairly difficult to detect on your computer so I got in the habit of powering down unless I need it to be powered up. I get in the habit, which is something that I learned from the intelligence community years ago and still employ throughout Washington, is I leave my phone outside of the room that I’m discussing things in. In DC, there are little cubbies outside of every conference room. You can just stick your phone in there. Nobody brings a phone or a computer that could be compromised into a sensitive discussion. If you care about those sorts of things, just leave your phone outside, power your laptop off when you’re not using it. With my Mac, it comes back on in 30 seconds anyway. In Windows, it’s a little bit longer but in my mind, it’s definitely time well spent.
If you’re going to talk about something that’s actually business important or highly sensitive, I encourage you to close the laptop clamshell and power off the computer. Share on XWhat if you have Amazon Echoes all around the house that are listening 24/7? Do you not have those? Do you just keep them outside of the room where you’re going to have sensitive discussions? How does that work?
I don’t have those in my house and I don’t turn on things like Hello Google and the other is Siri because of privacy concerns. Again, I was one of the early people to put a band-aid over my laptop cameras as well. That’s just me. I don’t want to take the risk. We know there’s a microphone and there’s an internet connection. There’s a risk so I just choose not to take it. In my mind, that trade-off is not good enough for me. But I am kind of jealous at some of the things I see in my friends using Siri and Okay Google for at home. I may get to that point but right now, the trade-off is not worth it for me.
What would you recommend for our listeners? Should they get rid of their Amazon Echo? I have an Amazon Echo, it’s just within a foot of where we’re recording right now.
Everybody’s got their own things that they consider sensitive that they wouldn’t want to get out. Maybe that’s a big business deal you’re doing, maybe it’s a personal preference, whatever it is, there are some things that I would whisper or otherwise [00:35:16]around any type of air party listening system.
Have there been cases where just regular people have been hacked and listened on?
Not ones where they’ve been compromised at this point. There’s a case now where I forget which brand it is that was listening in and it could maybe provide evidence of a crime that was being committed there. They’re looking to see if that’s admissible in court. These things do listen and companies do record them and they do then turn around and make money based on that information. Reputable companies like Amazon, Microsoft, and Google take great pains to talk about their privacy policies and talk about the privacy protections that they offer you, which are strong but not everybody in every chain is the same way but it’s encouraged people to be aware and look at who they’re doing business with, and who they’re trusting with their privacy, and what tradeoffs they’re making.
Any other steps in this process of hardening your security?
Last one is also easy and free. That is most people set their email so that if you get an image, if someone sent you pictures or an ad that includes an image, it automatically is displayed inside your email reader for your convenience. I turn that off, that automatic rendering off on mine just because I know that a lot of malware and almost all the advertising tracking information is now contained in those pictures. If you download it but don’t render the picture, you’re much better protected from both malware and adware than if you automatically load it. I will load very few images that come from a known source where I’m expecting to see an image. I got one this morning from a dealer that I wanted to send a request to and I expected those images. Then I just clicked on and loaded those images but by and large, I don’t load most images and honestly, that saves on bandwidth, that saves on storage and definitely saves the hassle of being tracked with adware and risk for malware.
Malware is sort of the more illicit stuff but adware is what makes the internet free.
Can you differentiate for our listeners the difference between adware and malware?
Malware is sort of the more illicit stuff but adware is what makes the internet free. All those free things that you like to do on the internet, you like to search, you like to play games, and you like to have social stuff, none of which has anybody ever asked you for money for. That is all paid for by advertising, by capturing your data and selling it to somebody else. In many cases, they anonymize it, which is what adware does. In many cases, they focus on you which is what malware does but it’s the same amount techniques in capturing that data and it is highly sophisticated stuff.
There’s a spectrum here of pretty innocuous adware, all the way to really egregious adware. I can think of one just off the top my head. It’s a video player and a video format that also installs this optional download, so the installer includes an option that they cleverly put the accept button right in the spot where you are clicking accept to everything else like install location as the default and all this sort of stuff and click, click, click, click, click and you just opted in for this nasty adware that gets bundled with this free software. It can be really hard to get rid of these nasty adware programs that you’ve inadvertently accepted and installed in your operating system.
It’s just easier to avoid first contact where you can. You’re not going to be perfect but you can cut way down if you follow these techniques. Cut way down in terms of how much this stuff actually touches you. It makes it just a lot easier, a lot safer to go through your online daily life.
Any tips for tools to remove adware or malware?
Take your time. It’s really hard. They make it hard on purpose. The honest companies make it difficult because they’re making the money off of you and the dishonest company is making [00:40:03] impossible. In many cases, you’re not going to get rid of all of it. The average person is not going to be able to detect what’s hidden on their computer. Antiviruses stops viruses but it doesn’t do anything about this kind of advanced malware type stuff. It’s really up to a professional to go through and that’s out of the price range of most consumers. The good news is people tend to change their devices every couple of years and you tend not to bring that stuff with you from device to device change so hopefully, people don’t have the oldest stuff. I do encourage everybody to accept the patches that come down. You get it with your computers. You get it with your phones. I know it seems like a hassle. “Jeez, they just asked me for patches.” These people would not be asking you for a patch unless they hadn’t figured out through someone else’s misfortune that there’s a hole in their program that’s being exploited. As soon as they figure a way to stop that particular way of attacking their clients, they want everybody to upgrade. Even though it’s a pain, I accept every patch that’s given to me by legitimate companies and get it in as soon as possible because you don’t want to be caught by a problem that the company solved a year ago, you just never got around to upgrading the operating system or patching the application.
Isn’t there a program that helps you remove adware? I think it’s called Adaware.
I just strongly advise doing whatever you can to avoid being infected in the beginning.
There is. It works to a good extent but it’s just a never-ending chase with the good guys and the bad guys so I just strongly advise doing whatever you can to avoid being infected in the beginning.
Yup, good tips. Any other steps in this process? We haven’t covered two-factor authentication for example. How many more steps do we need to go through to make sure that we don’t get our identities stolen and all that sort of stuff?
There’s so much more that individuals can do. At Unisys, we work a lot with the bigger companies that have consumers like banks where we’re moving quickly beyond the ID and password. In today’s day and age, it’s pretty commonplace to be offered two-factor authentication where your phone generally comes into play of reading an SMS number, answering a phone call, or pressing one or something like that. That’s pretty much rudimentary but now people are getting used to biometrics, they’re getting used to putting their thumbprints on the iPhone, they’re getting used to having Instagram look at their picture and recognize them. More and more, you’re going to start to see biometrics come in next instead of and in place of IDs and passwords. The real answer is where we’re headed in a couple of years. We’ve already got some leading banks around the world rolling this up to their clients but it’s in spots around the world. That’s what I would mention before, behavioral biometrics. That’s where we contract up to 100 different tiny, little aspects that we know about you from all that same stuff the adware captures about you, all that stuff that you’ve given out. We’re able to put together a risk score that says this probably is Steven or this probably isn’t Steven, or this is an 84% chance it is.
This can be based on Steven’s right-handed and he usually holds the phone in his right hand but whoever is typing it now is holding the phone on his left hand or he was just at this weird site on the dark web before he came to this site so that’s a red flag. He’s never been there before or he normally calls in either from his home IP address or his work IP address or any of these seven cell towers between his home and his office and yet this one is coming in from Croatia. There are all sorts of like 100 different factors that go into creating that risk score and it all happens behind the scenes, it all happens transparently. We now have clients that just turn on their computer and then try and go to a particular website, a banking website and they’re in as long as they’re expected, as long as it’s a risk score that says they can come in. They’re often running. Not even asked for an ID and a password which the bad guys are able to cut through like butter. It’s the future and it’s up to your companies to employ. It’s not a consumer-driven activity. It’s the consumer companies that will have to end up deploying it. Almost all companies, big companies, insurance, and financial services, energy, everybody that’s got big consumer applications are already looking at behavioral biometrics as the future.
Yeah, but in the meantime, until it’s been implemented in the companies that you are doing business with like your bank, having two-factor authentication is better than not, right?
For a bank, two-factor is absolutely better than one-factor.
For a bank, two-factor is absolutely better than one-factor.
Yup. It’s a pain to have your phone nearby and check what the code is that was texted to you.
Honestly, I don’t have a two factor set for things like Twitter because if they get it, they get it. I’ll reset it. Twitter knows who I am. I’m verified. I’ll get it back. But having it for bank accounts, having it for other high-value things that I do online, two-factor makes a lot of sense and it’s generally available from any service you’re looking for. It comes free. Google comes free with Facebook, it comes free pretty much with any social media app that you’re looking for. If you’re saying a lot of things online and you really don’t want to get out, A, you shouldn’t but B, you’re intending to do it anyway, upgrade to two-factor authentication. Use that phone that you carry around all the time anyway, and make that part of your identity.
Two-factor authentication is particularly important for Google and Facebook because so many of us use Google and Facebook as our login to other services. For example, you get in a prompt, you sign up for a new service and it says would you like to log in with your Google ID or your Facebook ID, or do you want to set a username or password. Personally, I always set a username and password so keep this in separate silos but a lot of people would just login with Facebook even though it’s a completely separate site. It has nothing to do with Facebook. Now, they’re putting all the keys in one place, really dangerous.
That’s back to that aggregation that I’m trying to avoid wherever possible. But in this case, these big ripped social media companies, really, they take your security very seriously, they take your privacy very seriously, they spend a lot of money upgrading and improving the privacy and security for their consumers. They know where their bread is buttered. They want the data but they don’t want anyone else to be able to get it or misuse it. It’s a delicate balance but definitely some great technology coming in. I think you’ll see behavioral biometrics coming out in social media before even some other companies with higher value information.
Any other steps in this process or shall we move on to some other questions?
Let’s go on.
What the heck is the dark web? Why should we care about the dark web? It sounds really mysterious and nefarious but what exactly is it?
Most people shouldn’t care but essentially it’s a way to use the same internet connections in an almost completely anonymous way. When you and I link, we’re using Skype today, there’s a record of it. My IP address in my office and this is in Georgia right now click to you and that’s a trackable, traceable connection with known Internet Protocol addresses. The dark web which is actually technically called TOR which is an acronym for The Onion Router, it’s a little inside joke. The dark web grew up because it’s a way to have the same level of you can go see anything anywhere but without any attribution in a, for a long time, completely anonymous way. What happens when you’re able to set up a store in a completely anonymous way? That’s where people sell things that aren’t quite legal in the real world. Drugs were originally sold heavily on the dark web and then guns and then nefarious services like murder for hire, all for sale on the dark web. That became the place to post if you figured out a way to hack into some other company, you could put that up for sale at the dark web because it would never come back to you. It couldn’t hurt you. People thought that they were anonymous.
Now, the good guys are finding ways to make that less of a hiding place, catching a little bit of light into the dark web.
Now, the good guys are finding ways to make that less of a hiding place, catching a little bit of light into the dark web. People should know few things about it. One, it’s massive. It actually outnumbers the addressable web that normal people would see. Two, everything is out there. It’s the wild, wild West of junk and every service under the sun. A lot of those services now are various law enforcement groups around the world masquerading. If you went on the dark web to try and hire a hitman, odds are you’d find one that’s actually a law enforcement person looking to find people trying to hire a hitman, same with a lot of the drug site and things. It’s huge, it’s out there and I do not recommend that the average person even try and go in. If you try and look around, you start to leave footprints. You’re just asking for attention from a lot of folks that like to do bad things. There are some real legitimate uses for anonymity and some real legitimate things happen on the dark web but unfortunately, they’re grossly outnumbered by the bad things that happen on the dark web and it’s just something people should understand it’s there but it’s not something they should have to interact with.
Yup. The currency that they’re all using on the dark web is bitcoin, right? Because you can’t trace that back to a person. It’s all very anonymous.
Yeah. There are a dozen or so different anonymous currencies they could use. Bitcoin is the most prevalent one today but this has been going on before bitcoin and will go on with other places as Bitcoin becomes more of a monitored currency. There are ways to pay for it without being tracked. There are ways to purchase things without being tracked. Like I said, wherever you can have anonymity, someone might be selling your mom’s apple pie but they might also be selling something much more nefarious.
Curious, do you have Bitcoin? I don’t. I’m not partaking in that kind of investment opportunity and I know people said, “Oh, I made tons of money off of it. I bought $10,000 of bitcoin and now, it’s worth $500,000.” I missed that boat. Is that something that you benefited from or something that you would recommend?
I love the underlying technology which is called blockchain which has a lot of really important uses in the world and has been invested in quite heavily to make inefficient systems more efficient and to make impossible things possible like a secure internet of Bings, which is going to be built on the concept of a blockchain. For Bitcoin, I never got into it for an investment but I was asked to do a speech a few years ago at Cal Poly, San Luis Obispo. I do a lot of general chats with students, try and get people into the security space. I thought I’d be dealing into an average college class and the professor was really right on. He’s like, “These kids are not what you expect. They’ve got a lot of questions.” They sent me a list of questions including what’s Bitcoin and how does Bitcoin work. I have read about it. I knew one of the early guys that have used it but I didn’t actually have a Bitcoin. I went online and I bought 20 bitcoins for $20 each just so I could use them at the speech. I figured out how they worked and talked about them. Now, those bitcoins that I bought for $20 are trading at about $1,000 so it turned out to be a pretty good payment for my speech. I sold a bunch of them off when they were $20 but there’s a coffee shop near where I live that still accepts Bitcoin for a latte. The last time I looked, .00007 bitcoin for a double latte. I think I’ve got caffeine for life out of the bitcoin craze but no, I’m not an investor in this space.
That’s funny. Did you mention earlier in the conversation about a dark web search? What exactly was that referring to? What is a dark web search?
There are ways to find things on the dark web but you have to build up a dark web reputation yourself in order to get allowed into many of these exchanges.
There are ways to find things on the dark web but you have to build up a dark web reputation yourself in order to get allowed into many of these exchanges. That’s their way of keeping out newbies and keeping out cops. You have to take some time to build up a reputation on some of these dark web sites and from that, you can get invited into some of these dark web spaces. There are ways to index that now and that’s where the search comes in. It’s different than Google but the result is somewhat the same. You are able to find places to buy whatever you want to buy, or sell whatever you want to sell, or trade whatever you want to trade. The technology underlying is very different but for the consumer, it functions in a similar way. However, this goes back to my original admonition, this is not a place for novices that somebody goes on and tries it, you’ll leave big, bright fingerprints pointing back to you and you just don’t need the attention from that crowd.
That makes sense. What about identity theft? I know there are things you can do in the offline world to protect yourself from identity theft like you can sign up for Lifelock or you can just do it yourself by every 90 days contacting the credit bureaus and setting a fraud alert so that it’s harder for the bad actors to steal your identity and create a credit under your account. What are some of the tips that you’d like to recommend?
Identity theft is getting more and more of a problem for civilization as we stand because your identity is worth a lot of money. Let’s say your health records are worth almost $100 to someone. There are a lot of people looking to steal them. Not from you probably but from the hospital, you just were in, or the doctor’s office, or the pharmacy. They all have access to that so identity theft is a big issue. I like systems that will track that on your behalf. I don’t like how much they charge for it and I don’t like some of the upsell techniques they use but I think having a third party look out for you is a valid investment now. We’re starting to see companies like banks and other places step up and take more care with you. And then there’s a new regulation that came out that starts to be enforced in 2018 called GDPR, the General Data Protection Regulation, which is really a global privacy regulation that starts to really impact companies with big fines. The smallest fine they’ve got is $20 million if they don’t take better care of their citizen’s privacy and consumer’s privacy. We’re seeing better improvements in taking care but identity theft is a real issue. It is, I’ll tell you, a pain in the neck to undo a stolen identity. These people move quickly. They move into your skin. They do things on your behalf like break laws so that you now have a record or don’t pay bills so that you now have debts. It definitely pays to watch what’s being done in your name. We’re recording this at tax season. It’s a very common thing. These people steal your identity and file tax returns before you do so that they get your refund and they’ll lie so it’ll look like a big refund. Not only do they get the money, the IRS comes back to you and says, “Hey, you were fraudulent in this. You owe us all this money back.” And you never got it in the first place so definitely do what you can to protect your identity. Do your part in some of those tricks and techniques that we talked about upfront of this podcast. It makes it harder for you to be the victim and then just watch who you’re giving the rights to and who you play with, online. Make sure it’s someone that you feel will take good care of your private information.
That’s great advice. One last question, you have a pretty high-level security clearance, super top secret whatever it is with the government. How do you get a security clearance and why would it be beneficial for somebody to have one and are there any downsides?
There’s a lot of downsides. The paperwork is incredible. I’ve gone through in my life. You get a security clearance granted by the government if you’re doing work that requires it and that’s the only way. The younger you are, the least amount of experience you have, the easier it is to get cleared because you have to have led a pretty clean life so there are definitely things that I’ve missed out on that some of my friends have partaken in over the years. I’ve had a clearance since I was a teenager. Absolutely, there’s cost. I do a lot of talking to high school students across the country and actually around the world. One of the things that I tell them, if they’re interested in technology, they should get interested in security if they want to make more money because a security programmer makes 50% more than a regular programmer and it’s not any harder. And then I tell them if they choose to lead a clean life and not get young juvenile record for things like smoking pot or too many car chases or sort of juvenile things, shoplifting, those kind of things that kids often get into, if you choose to not do that and are able to get clearance at a young age, you’ll make 50% more on top of that so you can make double with the same set of skills that your friends are graduating with if you choose to get into security technology and be clearable. But then the next step is to apply for jobs that require it and find a company that’s willing to sponsor you through the clearance process which is not free. It’s free to the person but the company pays and then you have to have a high expectation of getting cleared. However, it is a great way to see what’s really going on in the world and be able to use your brain and use your capabilities in a way that’s able to have a positive outcome for a large group of people that really need it.
The downside though would be that you’re basically monitored for life in a greater capacity than you would be as a normal citizen, right?
It depends on your level of clearance, low level of secret clearance. There’s every seven years, they talk to your neighbors. They talk to your friends and they see if you’ve done things that might make you a higher risk factor. I still can’t go to Cuba and be a scuba diver. A lot of my scuba diving buddies go to Cuba. I still can’t go because the clearance says. There are some travel restrictions but mostly, it’s just a lot of paperwork and clean living. I’m used to the clean-living part and never got used to the paperwork piece but it’s a necessary evil to be able to do my job at a high level.
Awesome. Thank you so much, Tom. This was really insightful and fascinating. What a different world and what we tend to think about on a daily basis and you live in this world. It sounds pretty exciting. Jason Bourne-like, I guess. Thank you, Tom. Thank you, listeners. We’ll create a checklist of actions to take based on the recommendations that Tom gave in the episode. This is Stephan Spencer signing off. We’ll catch you on the next episode of Get Yourself Optimized.
Important Links
Connect with Tom Patterson
Tools/Apps
Organizations/Companies